Technology and Process Change.
-
Using Storytelling for IT Initiatives
Stories shape how employees experience change—use them to reframe resistance, spark engagement, and turn IT initiatives into something people believe in.Improve engagement, adoption, and performance through stories.
“This new system is going to eliminate our jobs.” “This system will increase my workload.” “I don’t need to use this system – I have everything I need in Excel.”
Sound familiar? These are the messages your people tell themselves about your project. They sabotage your implementation. It’s time to change the narrative.
What Stories Do for Your Initiative
Create the right mindset.
We naturally tell ourselves stories to make something new seem familiar. What’s familiar can be either good or bad – we’re subconsciously looking for context to interpret the experience.
For years, the members of the Academy of Motion Pictures Arts and Sciences chose their Oscar nominees by paper, submitting ballots that had to be manually counted. But in 2012, they decided to introduce a new system for electronic voting. When the team asked members what people were saying about the new system, they learned that people were comparing it to the movie “Recount” – a story about the 2000 US presidential election, and controversy over voting machines.
That story was familiar, but not helpful. The team needed Academy members to have the right mindset. So, the team began telling members stories about the evolution of film — moving from silent movies to talkies to digital – like the movie Avatar. This familiar story reframed the change as something good, exciting, and inevitable.
If our goal is adoption of a new system, we need to create an openness to what’s happening next by capturing imagination, taking users on a journey, and cultivating a positive emotional response.
Promote organizational culture and values.
Your initiative is happening in the context of your company’s culture. Telling a story that aligns with that culture reduces resistance and further strengthens what’s best about your company.
For example, when Kindercare introduced a new service system for child check-in and payment, they could have told stories about employees being efficient and operationally excellent. They didn’t. They instead told stories about employees being able to care and connect – which synced with their values and culture — and how this new system would make care and connection possible.
Boost engagement and motivation.
Great stories answer the question, “Why should I care?” Stories make technical content more compelling.
When Netflix moved to the cloud, they shared stories about common issues with their current infrastructure, like outages during peak viewing times, and the need to scale during new season releases. They used relatable metaphors, like “packing for a move” or “expanding a living space” to introduce technical IT concepts.
By framing information within a story, we illustrate how new systems or processes impact the real-life work of employees, making the content more relatable and interesting.
Help employees remember what they learned.
The human brain is naturally wired to remember stories better than abstract concepts or isolated facts. This is because the brain’s visual and sensory processing areas – which we use when we’re listening to stories — developed long before the parts that handle language and symbolic thinking.
Our brains use two systems, verbal and non-verbal (visual), to process information. When we hear or read a story, we engage both systems. That’s because stories often create mental images. Lists, acronyms, or data, tend to activate only the verbal system. Engaging both systems makes recall much easier.
One study showed that people are up to 22 times more likely to remember information when it is embedded in a narrative rather than in a list of facts.
This means that employees who learn about new systems through stories are more likely to retain and use the information effectively.
Why Stories Work
Brain Evolution
We evolved a brain with three parts: the reptilian survival brain, the limbic emotional brain, and the neocortex thinking brain. Information flows from the inside out – from survival, to emotional, to thinking. Emotions come before thoughts. We make decisions based on emotion and come up with reasons afterward. So, stories, which stimulate emotions, are great for persuading people to make a decision or take an action.
Mirroring
Research using fMRI demonstrates that listeners’ brains sync with the storyteller’s brain; areas of the storyteller’s brain that are active while telling the story become active in the listeners’ brains after a short delay.
Dopamine
Stories are great combining emotion with information. They trigger the brain’s reward system, which releases dopamine and makes us feel good. Dopamine is linked to memory, so it helps us remember the information in the story.
Cortex Activity
Stories activate multiple areas of the brain, emotion centers, motor cortexes, and visual processing centers. To some extent, when we hear a story, we live it. Our brains simulate the events and actions in the story, including the sensations and feelings that go with it. A story we hear becomes our own experience, and that rich experience sticks with us.
How Should You Begin?
- Ask yourself, what stories are already out there? Better yet, ask people around you. People are telling stories about what happened before, what is going on now, and what they expect in the future. You need to know what’s out there to either use it or address it.
- Determine what familiar things you can hook into. What do your users have in common? What are their shared experiences? Start there – your stories will gain momentum more quickly.
- Don’t be afraid of negative stories. They capture attention because of our innate fear of risk. Can you tell a story about the consequences of failure? For example, if your users all experienced the same failed cutover you can, and must, explain how this time it’s different.
- Grab their attention. Include detail, names, and real-life struggles! The more specific it is, the more memorable it will be.
Stories just work. They are fundamental to how we operate as humans. If we tap into the stories our users are telling themselves, and guide them to the right stories, we can shape the narrative and make IT implementations easier and more successful.
Click here to download our quick reference tool to help you build your own stories.
Want to explore this topic in more detail or learn more about Emerson? Hop on his calendar: Book a meeting with Rich
-
The Digitally Literate Workforce
When employees truly understand their tools, technology stops being friction and starts fueling innovation. Build digital literacy to unlock your workforce’s full potential.Get the synergy you need from your tech and your people.
In most organizations, the tech stack is bigger than the skill stack. You’ve got collaboration suites, AI, automation tools, CRM platforms, data dashboards…and a workforce that’s still not quite sure how to get past the basics.
The result: expensive tools, underused features, and innovation that stalls in favor of business as usual.
Digital literacy shouldn’t be a daunting term. It isn’t about teaching everyone to code. It’s about helping people understand their tools well enough to do great work and imagine better ways of working.
A musician has a path to great performance. They learn the basics of their instrument. They practice for a long time. They get so fluent that they finally understand what the instrument can do – how it can be used to interpret a composition and convey meaning to the listener. That’s where the instrument is really valuable – in the hands of someone who really knows how to use it.
Your employees need a level of familiarity with their digital tools before they can truly perform.
When the tools get out of the way, the work gets better.
In a digitally literate organization, technology is a means to an end.
- People don’t think, “How do I format this?” They think, “What’s the clearest way to tell this story?”
- They don’t ask, “Where do I click to get the report?” They ask, “What decision are we trying to make?”
- Meetings aren’t spent troubleshooting; they’re spent problem-solving.
That only happens when people are confident and fluent in the tools they use every day. Until then, technology is friction. And friction kills performance.
Digital literacy is a prerequisite for innovation.
Leaders often say, “We want people to innovate. Our technology will help.” But until employees truly understand their tools, they won’t innovate beyond their function.
If I barely know how to use our collaboration platform, I’m not going to rethink how my team shares knowledge. If I don’t understand the basics of data visualization, I’m not going to propose a better way to share performance insights. I’ll stick to the old way, or just use the new tools to offer a shinier version of emails and spreadsheets.
Digital literacy unlocks three big shifts:
- From compliance to creativity. People stop doing it the way the system says to do it and start asking, “What else could this system do for us?”
- From local optimization to cross-functional innovation. Once employees truly know their tools, they can more easily see how a feature or workflow could help other teams, customers, or business lines—not just their own.
- From IT-pushed change to business-led innovation. When Business understands what’s possible, they stop waiting for IT to drop new features from above. Instead, they bring informed ideas to the table and co-create solutions.
Rethink the IT–Business relationship.
In many organizations, IT is seen as the feature factory and the help desk. Business leaders ask, “What’s coming in the next release?” or “Can you fix this?”
But the dynamic you actually want is:
- Business drives innovation based on strategy, customer needs, and frontline insight.
- IT meets those needs and brings synergy with new ideas and collaborative, informed solutions, often using tools you already have.
- Together, the Business and IT decide when new functionality or adjacent products are truly needed.
This is only possible when employees and business function leaders have enough digital literacy to have a real conversation with IT — not just present a list of complaints or requests, or blindly accept the next update or tool.
Build digital literacy that actually changes behavior.
Here are five practical ways organizations can raise digital literacy and improve collaboration between IT, employees, and business leaders.
Treat digital literacy as a core competency.
Digital skills shouldn’t live in optional training modules that people get to when they have time.
- Build digital fluency into role expectations, performance goals, and development plans.
- Include digital skills in leadership competencies. (“Can you lead a digitally enabled team?”).
- Recognize and reward employees who simplify processes or innovate using existing tools.
When digital literacy is part of “good performance,” people make time for it.
Start with real work, not generic training.
Most digital training fails because it’s tool-centric and abstract. They get a “feature tour” and forget what they saw by Monday. Instead:
- Design learning around real, role-based scenarios: “How do we streamline approvals?” “How do we share project status without email threads?”
- Have teams bring live work (reports, workflows, decks) into training and improve them in real time using the tools.
- Make “before and after” examples visible so people see the payoff.
If employees can immediately use what they’ve learned to make today’s work easier, it’s real. You build momentum and buy-in.
Turn power users into internal coaches
Every organization has those people who quietly figure things out and help others. Make that informal support system official and visible.
- Identify “digital champions” in each function or business unit.
- Give them extra training and early access to new features.
- Ask them to host short, targeted sessions (like, “15 minutes to cut your reporting time in half”) and serve as go-to resources on their teams.
This keeps support close to the work and it humanizes digital learning. People are more likely to ask a peer than open a ticket.
Bring IT into the business and the business into IT
To move from “IT vs. the business” to one team:
- Invite IT to observe workflows, attend team meetings, and hear pain points directly.
- Include business leaders in technology roadmaps so they can weigh in on priorities and use cases.
- Co-create design sessions or pilots where IT, end users, and business owners shape the solution together.
The goal: IT isn’t just deploying tools; they’re solving problems with the people who own and live those problems.
Implement digital literacy with change management
Digital literacy is not just training. It’s change.
- Make a clear case for change: Why does digital fluency matter to our strategy, customers, and employees’ day-to-day lives?
- Use the essentials of change management: active sponsors, consistent messaging, tailored stakeholder engagement, realistic role-based training, measurement, and sustained reinforcement.
After training, measure behavior, not just logins:
- Are people using features that reduce manual work?
- Are cycle times improving?
- Are teams experimenting and sharing what they learn?
When you deliberately manage the change, digital literacy starts becoming part of your culture, not a one-off initiative.
The payoff isn’t just capability and performance; it’s readiness.
High digital literacy does more than help people use today’s tools. It makes your organization ready for what’s next.
When a new feature, adjacent product, or platform comes along:
- Employees already have the confidence to explore and learn.
- Business leaders know how to ask, “How could this help us deliver our strategy?”
- IT is plugged into real needs and can respond with solutions, not just more layers.
In other words, you don’t just adopt new technology. You use it to create new value.
We have a major retail food products client who operates globally. In their Mexico operation, they switched from standard IT reports to self-service Power BI reports. The problem: their existing reports didn’t reflect what the organization really needed. As a result, employees spent over 120 hours each month upgrading those reports — cleaning, reformatting, and calculating new indicators that were actually useful.
But as soon as these digitally savvy employees had access to the data in their new tool, Power BI, they created new reports and calculations directly in that tool. They suddenly had the views, formats, and indicators they needed. They saved that wasted time and instead spent it on creating new reports and views, as needed. The synergy between the powerful tool and digitally literate employees saved useless effort, reduced response time to leadership, and lowered complaints and requests to IT.
That’s the difference digital literacy makes. It’s not about mastering every system. It’s about giving people the confidence and fluency to focus on what actually matters: the work, the customer, and the future you’re trying to create.
-
AI and the Quest for Truth
Learn five smart ways to use AI responsibly—and keep misinformation from derailing your credibility.How Professionals Stay Smart in the Artificial Intelligence Age.
A user once asked a generative AI tool to come up with an original idea for children using a Lego set. The tool’s answer: “Imagine a Lego set that allows you to build a fully functioning time machine with intricate details and moving parts. This set combines the fun of building with Legos with an educational twist, teaching kids about historical eras and famous landmarks as they embark on time-traveling adventures.” What? Imagine the health hazards, the lawsuits, the damage to our current timeline…
Ok, that’s a delightfully harmless example. (Well, until we invent time travel anyway.) But misinformation isn’t always so obvious.
And we need to know when AI gets things wrong, because the consequences can range from funny to embarrassing to catastrophic.
Inaccurate data, flawed guidance, or hallucinated case studies can erode trust, trigger poor decisions, and damage your relationship with your team or your customers.
Nowadays, we pretty much have to use artificial intelligence, right? From generating marketing content to summarizing research and writing code, AI is saving time and unlocking creativity. It feels like if you’re not using it, you’re a step behind.
The good news: you can harness AI’s power without falling victim to its little robot lies.
The Misinformation Problem
The term “hallucination” is often used to describe when generative AI tools produce information that sounds plausible but is oh so wrong. These tools are powerful language models, not search engines. They don’t take a skeptical view or verify sources. They predict language based on patterns, not validity.
In 2023, a New York attorney used ChatGPT to draft a legal filing that cited six entirely fabricated cases. The AI-generated cases didn’t exist, but they looked real enough to pass an initial glance. The result? Sanctions and professional embarrassment. (Source: NYT)
Think about the high-stakes situations you might confront:
- A strategy deck citing false data could mislead executives and derail decisions.
- An AI-written employee communication could spread confusion if it includes misquotes or outdated policy references.
- A government contract could be rejected if AI invents credentials or claims.
Misinformation doesn’t always look like fiction. It often seems credible.
Three Traps for Business Professionals
Overtrusting Output
AI sounds confident. Its tone is polished. But confidence is not accuracy. (We all know people who fit this profile, right?) Professionals pressed for time might generate, copy, paste, and trust without verifying.
A psychological dynamic called “authority bias” is to blame: we tend to trust information from sources that “sound” authoritative, even if they aren’t.
False Citations or “Source Laundering”
Some generative AI tools fabricate sources or mix real citations with fake ones. Even when sources are accurate, they may be out of context or misrepresented.
In one test, ChatGPT cited a Harvard Business Review article that didn’t exist, but with a title and author combination that seemed plausible.
The Chicago Sun-Times published a 2025 Summer Reading List recommending 15 titles. The problem: ten of them were not real. The journalist relied on a third-party source that had used AI to generate the list.
A separate news item found that if you ask Chat GPT for links to sources, and there aren’t any, it will simply make them up.
Context Collapse
AI lacks situational awareness. It may pull ideas from unrelated fields or fail to consider the unique regulatory, cultural, or industry context that matters in your decision-making.
Five Ways to Stay Smart and Safe with AI
Always verify sources.
If AI offers a citation, check it manually. Follow the link. Search for the document. If it doesn’t exist, that’s your first red flag.
Pro Tip: Use AI tools like Perplexity.ai or Consensus.app, which prioritize sourcing and transparency over polish.
Add a layer of human judgment.
AI can accelerate your thinking, but it should not replace it. Ask yourself:
- Does this make sense in our context?
- What’s missing?
- Who would be harmed if this were wrong?
Think of AI as your intern, not your expert advisor. Its job is to help you think, not to do your thinking for you.
Use AI transparency settings.
Tools like ChatGPT Enterprise or Copilot often offer audit trails or cite where their information came from. Use these features to assess credibility.
If you’re using AI inside your organization, push vendors to explain how their models generate outputs and what guardrails are in place.
Insist on a human in the loop.
In regulated or high-stakes industries (e.g., healthcare, finance, government), build processes that require human review before AI-generated content is published or decisions are made.
This aligns with the GROW coaching model: AI may help define the Goal and assess Reality, but Options and Will must come from human insight and accountability.
Train teams to spot and stop AI misinformation.
Embed AI literacy into onboarding, upskilling, and leadership development. Teach employees:
- How to question AI output
- What to verify (and how)
- When to escalate concerns
And remember what we change management pros preach: changing behavior requires awareness, engagement, action, and reinforcement.
The Enemy
It’s not generative AI. Complacency is the enemy.
Generative AI isn’t malicious. It’s simply not designed to be truthful. It’s designed to be useful. As business professionals, it’s on us to pair AI’s speed and creativity with our discernment and ethics.
The most dangerous misinformation isn’t always the most outrageous. It’s the quiet, almost-right statement that slips through our filters because we’re too rushed, too trusting, or too dazzled by the tech.
In the age of AI, wisdom isn’t knowing everything. It’s knowing what to double-check.
-
The Sweet Spot
Stop chasing every skeptic — find your change sweet spot and win where it counts.A Simple Accelerator for Change Communications.
People resist change. You’ve heard it, read about it, and experienced it first-hand.
But you have a big change initiative upcoming in your organization. Maybe it’s a new technology, an acquisition, a new process… You’ve already heard people don’t want it. They want things to stay the same.
So, you’d better start turning that resistance around, right? Winning the hearts and minds of everyone you need to adopt this change.
Not so fast. You don’t need to combat resistance on every front. You don’t need to reach everyone, just your sweet spot.
Don’t waste time on those dead set against this change. They’ll never come around, and you don’t need them to.
Don’t waste time on those who are already on board. You will be, as they say, preaching to the choir.
Spend time on those in the middle – mildly supportive to mildly resistant – and who matter when it comes to the success of your project.
That’s your sweet spot. Get them, and you’ll win.
- Identify your stakeholders. Group them in whatever way makes sense for your project: by business unit, function, role, and/or geography.
- Map them. To do this, figure out two things: their level of resistance or support of the change, and their level of influence on the success of the change.
Here’s an example grid you can use to map your stakeholders.
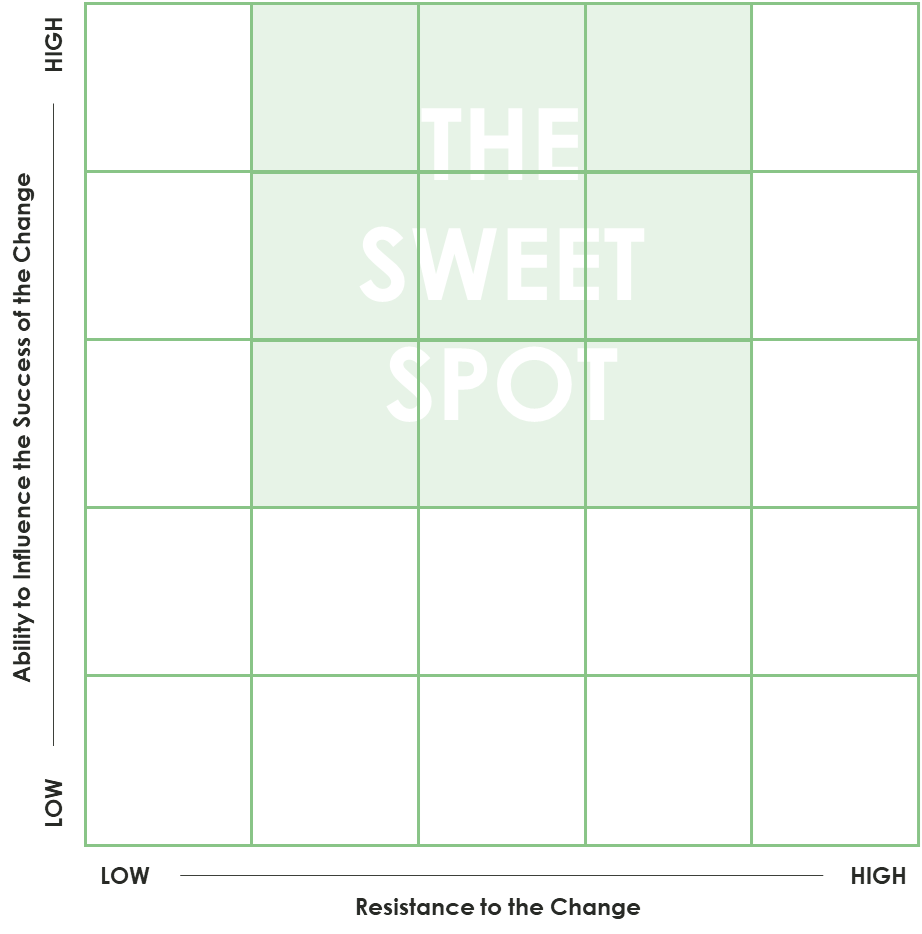
As you can see, the sweet spot includes those who can influence your success, and those who are not firmly for or against. Focus your energy there.
- Engage the sweet spot. To start, you need to understand each group in your sweet spot.
- What do they care about? How does this change address those things?
- What are the benefits and opportunities for this group?
- What challenges will the change pose for them?
- What are the consequences of non-compliance?
- What channels do they prefer for engagement and communication?
- What kinds of words or images appeal to them?
- Who are the people who influence them?
- What is their history with similar changes?
Answering those questions will help you craft an “experience plan” for each group, to begin moving them from awareness to engagement to adoption to ownership.
So, do you ignore the hecklers? No. Give them all the support you are giving employees in their stakeholder group, like communication, training, and post-launch support. Just don’t spend extra energy trying to turn them around.
This is different from what I was originally told years ago. “Find the naysayers and turn them around. Naysayers will tell you where your blind spots are. They will ultimately be your biggest advocate.” The research says otherwise. Most of the naysayers won’t get on board.
As you engage the sweet spot and the momentum shifts toward your change, the highly resistant will quiet down or change their minds.
Consensus is not the goal. Adoption, ownership, and performance are the goals. Every person in your organization doesn’t have to agree with every decision made. But if it’s a sound decision, you need to make its implementation a success.
-
The Skills AI Hasn’t Replaced – and Why Your Future Depends on Them
AI may boost efficiency—but can it replace the experience that builds leaders?If AI is the future of work, why are we designing away people who do the work?
The business case for AI is efficiency. That usually means fewer jobs.
Dario Amodei, CEO of Anthropic, warned Axios that AI would lead to the “mass elimination of jobs across technology, finance, law, consulting and other white-collar roles, especially entry-level gigs.”
Noam Scheiber, from the New York Times, found that experienced workers aren’t safe either – companies are questioning the need for costly oversight when AI can make cheap labor more productive.
Whether we’re rookies or veterans, the financial incentive is clear: the organization will be leaner.
Traditionally, people grew into leadership by moving through roles that gave them critical on-the-ground experience. But today, those foundational roles are the first to be automated.
Are we eliminating the lived experience that feeds our leadership pipelines?
TaQuonda Hill, a senior information technology transformation leader, and I discussed the potential impact on succession planning and talent development.
The Irreplaceable Skills
Repetitive tasks have value. Flipping burgers, writing procedures, researching case law, or calming angry callers builds something more enduring than muscle memory. These experiences teach us how to lead.
Among the lessons:
Empathy. If you’ve done the job, you understand the people who still do it. It makes you more relatable — and more effective. Empathy is the foundation of connection.
Grasp of Implications & Context. You don’t know what you don’t know. But when you’ve done the work, you’re more likely to anticipate unintended consequences. Consider Boeing’s 737 Max crisis. Leadership outsourced critical engineering oversight for speed and savings. But without the institutional memory and technical fluency, they missed the risk. Tragic results followed.
As TaQuonda put it, “When you strip out the context, you gut the leadership pipeline. You might gain speed, but you lose the lived experience that turns managers into leaders.”
Team Development. People don’t scale. Teams do. And good teams are built by people who know how to work through complexity. One of my first summer jobs was at Burger King. A colleague made a point of slinging hot oil my way. It wasn’t fun. But it was formative. I learned to navigate conflict and win people over without authority.
As TaQuonda put it, “AI can make work transactional. But leadership isn’t transactional – it’s relational. If we raise a generation of leaders who’ve never had to influence, inspire, or navigate uncertainty, we’ll lose what makes them credible.”
Cultural Awareness and Navigation. Knowing what will and won’t work in a given organization takes experience. Call it politics if you want, but it’s how things get done. Being right isn’t enough. You have to understand the system you’re in, and how to move within it.
The fantasy is that tech will replace people. The reality is that it replaces undifferentiated effort. This leaves us with a greater need for people who can think, adapt, and scale others. Insight comes from experience, and we’re cutting the very roles that grow it.
The Risk of Outsourcing Potential
Traditionally, leadership was forged in the trenches: prioritizing under pressure, communicating across silos, and failing forward. Early-career roles weren’t glamorous, but they offered repetition, feedback, and the slow build of judgement.
If we are not careful, we’ll eliminate this development stage entirely. More than ever, leadership development must be intentional.
TaQuonda believes that “Leadership development needs to be treated like product development – intentional, resourced, and iterated. You can’t outsource wisdom.”
“Some organizations are building escalators – fast, effective AI-driven paths to decision making. But real leadership is built on stairs: deep skills, context, and ability to tell a story because you’ve lived it.”
And that’s the key. “Talent is currency,” TaQuonda adds. “But it’s not about what skills someone has – it’s about the impact they can deliver. That’s what leaders need to recognize and grow.”
What Great Organizations Are Doing
According to TaQuonda, we’re still learning where AI fits into our organizations. “It’s not Big Bang. It’s iterative. We start with buttons, not blueprints.” That means evolving not just the technology, but how we lead through change.
“We’re used to investing in tech labs to drive innovation,” she notes. “Maybe it’s time we invested in leadership labs to do the same for judgement, storytelling, and behavioral skills.” In this new model, learning isn’t confined to training sessions; it’s embedded in the work. “We don’t just train – we rotate, experiment, and test. You build it, you run it. That creates accountability.”
The Takeaway
It might look like we’re outsourcing our bench. In reality, we’re weakening our succession plans.
AI is here. But our future depends on human leaders.
We can outsource tasks. We can’t outsource wisdom.
-
Authenticity in the Age of AI
Five ways government agency leaders can stay authentic and effective in the age of AI.A Public Sector Leadership Imperative.
I recently read a departmental memo that struck all the right chords, clear, empathetic, visionary. But something felt off. It was too polished.
As it turns out, the memo was AI-generated. It made me pause and reflect: in a world where communication can be simulated at scale, what does it mean to be authentic?
For public sector leaders, this question isn’t philosophical, it’s practical.
The New Authenticity Gap
Artificial intelligence is changing the landscape of leadership. From policy briefs to constituent outreach, AI tools can now mimic tone, sentiment, and insight with remarkable fluency. But imitation isn’t connection.
In public service, trust isn’t earned through perfect prose, it’s earned through presence. Through consistency. Through leadership that feels grounded in real values and experience.
The risk is this: as the tools get better, the human voice becomes harder to distinguish and easier to question.
Public servants and employees are already predisposed to skepticism. Negativity bias tells us that people tend to focus more on what feels false or manipulative. Add in confirmation bias, and you’ve got a workforce that may interpret overly polished AI-generated messages as just more evidence of top-down detachment.
What Does It Mean to Be Authentic?
Let’s get practical. Authenticity isn’t about oversharing or rejecting innovation. It’s about alignment between what we believe, what we say, and what we do.
In change leadership, it’s called the “Say-Do Gap” — the space between what leaders say they value and what their actions demonstrate. Authenticity is about narrowing that gap.
Why is this so important now?
- In times of transformation, when budgets are shifting, roles are evolving, and systems are being reimagined, this alignment is the foundation for real trust.
- In high-stakes, high-scrutiny environments like the public sector, this alignment is everything. Employees and constituents are watching closely. “Do you mean what you say? Will you follow through?”
When there’s a mismatch — when messages feel manufactured or disconnected from reality — the trust erosion is fast and hard to reverse. But when words and behaviors align over time, even imperfect communication carries weight.
How Public Sector Leaders Can Stay (and Feel) Authentic
Here are five practical ways to embrace both technology and human nature to effectively lead in the evolving age of AI:
1. Be transparent.
You don’t have to disclose every tool used, but when appropriate, naming the role AI plays in your communication can build trust, not erode it. People appreciate honesty over polish.
2. Don’t outsource your voice.
Generative AI can be a powerful first draft partner. Use it to save time, explore tone, or structure messages. But let your lived experience and leadership point of view shape the final product. If it doesn’t sound like you, it won’t feel like leadership.
3. Practice strategic self-disclosure.
Public servants aren’t looking for confessions; they’re looking for context. When you share a personal experience that aligns with a policy, priority, or pain point, it signals empathy and being grounded.
4. Lead with consistency, not performance.
Authenticity isn’t a one-off act, it’s cumulative. As your words and actions align over time, you will build goodwill and trust. This “conversational capital” becomes especially valuable during times of high-stakes change.
5. Prioritize presence over perfection.
Flawless communication isn’t the goal. Feeling seen and heard is. Sometimes the most effective thing you can do is show up, listen actively, and speak from the moment even if it’s not fully scripted.
The Human Advantage
AI can replicate tone. It can scale messaging. But it can’t lead.
It doesn’t carry the weight of responsibility, the courage to be vulnerable, or the insight that comes from years of public service. Those are the things that make leadership human. And in this rapidly evolving age of AI, they’ll be the things that make leadership matter.
By the way: I used AI tools to support the drafting of this post, but all ideas, insights, and final edits are my own.
Want to explore the topic in more detail with John? Hop on his calendar: Book a meeting with John
-
5 Reasons You’re Not Getting the Most from AI
Turning AI Potential into Real Business ValueAnd How to Do AI Better.
Artificial Intelligence has the potential to transform how organizations work, innovate, and serve customers. Yet many leaders find themselves underwhelmed by the results of their AI initiatives.
In fact, new data from MIT show that 95% of AI pilots are delivering zero measurable return!
Why? Because the problem usually isn’t the technology. It’s how you’re using it.
Here are the five biggest mistakes:
1. Your data isn’t ready.
The old adage applies: garbage in, garbage out. If your data is messy, inconsistent, or incomplete, AI can only amplify those flaws.
- Is your data structured in a usable way?
- Are you using a data lake or other scalable storage strategy?
- Did you flood your LLM with everything you had, without cleaning, tagging, or segmenting it by relevance?
Raw data without curation leads to weak insights. AI’s output is only as strong as the input it’s given.
2. You implemented without a strategy.
Too often, companies pursue AI simply because everyone else is doing it. That approach almost guarantees disappointment. Successful AI adoption requires:
- A strategy aligned with business outcomes.
- Clear metrics for value (beyond “hours saved”). Think faster time to market, improved customer experience, or stronger employee engagement.
- A focus on use cases, not hype. AI should solve real business problems, not be a vanity project.
If you deployed AI without knowing the problem you wanted it to solve, you’re wasting your investment.
3. You didn’t prepare your people.
AI changes how people work. It requires different ways of thinking, new workflows, and new communication patterns. If your workforce hasn’t been:
- Trained in how to interact with AI,
- Guided on how their roles will evolve, and
- Supported in building new skills
…then you’re in for employee resistance and underperformance.
4. Your prompts (and people’s AI literacy) are weak.
Large language models don’t just “know” what you want. They need to be guided. That’s where prompt engineering comes in. It’s an art as much as a science. Weak, vague, or overly broad prompts generate disappointing results. Strong prompts, by contrast, can unlock nuanced, actionable insights.
But prompts don’t live in a vacuum. Without AI literacy, your workforce won’t understand how AI works, its limits, or its ethical considerations. Teaching people how to think critically, ask better questions, and apply responsible practices is the foundation of writing better prompts.
5. You underestimated change management.
AI adoption isn’t just about technology; it’s a change initiative. Like any organizational change, it requires leadership sponsorship, communication, and reinforcement.
And here’s the critical piece: storytelling. You must tell AI success stories in a way that makes employees feel part of the journey.
Numbers and technical jargon don’t inspire people to change behavior — stories do.
When leaders frame AI as a story of empowerment, growth, and human/AI collaboration, adoption accelerates and resistance fades.
Done well, storytelling removes fear. It helps employees see themselves as an essential part of the organization’s future.
AI success doesn’t come from buying the latest tool or chasing the latest trend. It comes from laying the right foundation:
1. Clean, structured data.
2. A clear strategy with measurable outcomes.
3. People who are prepared, skilled, and literate in AI.
4. Strong prompts fueled by critical thinking.
5. Change management fueled by storytelling.
Organizations that master these fundamentals are the ones realizing AI’s full potential – and the ones who won’t be left behind.
References:
Chari, P., Challapally, A., Pease, C., Raskar, R., & Nanda, M. (2025). State of AI in business 2025. Project NANDA / MIT.
Perry, J. M. (2024). The AI evolution: How leaders can build an AI-native organization. Vibes AI Press.
-
Why Most AI Projects Are Failing
How to avoid the most common pitfalls.You can win if you avoid these pitfalls.
We’re all witnessing the transformative potential of Artificial Intelligence (AI). From streamlining operations to unlocking new customer insights, the promise is immense. But as many business and IT leaders are discovering, turning those AI dreams into reality can be a bumpy ride.
How often do AI projects actually succeed? According to research by Harvard Business School’s Iavor Bojinov, the current success rate of AI projects hovers around a sobering 12%.
The current ROI on most AI initiatives is overwhelmingly low.
Leaders are compelled to invest based on AI’s ethereal promise, but in the short term, the current financial returns are just not there.
So, how can we buck this trend and ensure AI initiatives deliver tangible results? Bojinov’s insightful work, including his HBR article Keep Your AI Projects on Track, provides crucial guidance for leaders.
The Pitfalls and How to Avoid Them
Bojinov’s research highlights several common challenges that derail AI projects.
- Lack of Clear Business Objectives: Many initiatives kick off with the “cool” factor of AI rather than a specific problem to solve or opportunity to seize.
To overcome this temptation, start with a clear business need. Don’t let the technology lead; let the business strategy drive your AI efforts.
Ask, What business outcomes are we trying to achieve? How will AI help us get there?
- Data Dependencies and Quality Issues: AI thrives on data, but often the data is siloed, messy, or insufficient.
Leaders must understand the data landscape early on. Invest in data infrastructure and governance, as a big chunk of an AI project timeline is often devoted to data preparation.
Ask, Do we have the right data, in the right format, and of sufficient quality to train and deploy our AI models effectively?
- Talent Gaps and Integration Challenges: Integrating these solutions into existing systems and workflows can be a major hurdle.
Building and deploying AI solutions requires specialized skills. Take a multidisciplinary team approach that bridges the gap between business understanding, data science expertise, and IT capabilities.
Ask, Do we have the right talent in place, or a clear plan to get it? How will our AI solutions integrate with our current technology stack and business processes?
- Traditional IT Development Approaches: Long projects with a broad scope put AI projects at risk because they lock you into a solution from the start.
AI projects are often exploratory by nature. First, AI innovation is moving fast, so you’ll want to take the latest thinking into account. Second, you need to test and confirm what works for your company. Using an iterative or Agile approach, you can bring in new ideas midstream and “fail fast” to land on the best outcomes.
Ask, How can we create a nimble project? What mindsets and processes do we need to innovate, test new solutions, and incorporate lessons learned?
- Overlooking the “Human” Element: Resistance to change, lack of trust in AI-driven insights, and inadequate training can all hinder adoption.
AI implementation isn’t just about technology; it’s about people. Bojinov underscores the need for change management and clear communication. For example, engage stakeholders early and often. Focus on how AI can augment human capabilities rather than replace them.
Ask, How will we prepare our employees for these changes? How will we build trust and ensure the adoption of AI-powered tools and insights?
The Takeaways for Leaders
Bojinov’s work provides actionable insights for successful AI initiatives:
- Focus on business value first. Define specific, measurable business goals before diving into technology selection.
- Prioritize data readiness. Invest in your data infrastructure and ensure data quality is a top priority.
- Build collaborative, cross-functional teams. Foster communication and collaboration between business, IT, and data science teams.
- Embrace iteration and agility. Adopt an agile approach that allows for learning and adjustments along the way. Break down large projects into smaller, manageable milestones.
- Don’t forget the people. Plan for change management, communication, and training to ensure successful adoption.
The potential of AI is undeniable, but realizing that potential requires a strategic, business-driven approach. By learning from the challenges and adopting these principles we can improve the success rate of our AI initiatives and unlock the true value of this transformative technology.
-
Three Things Your AI Strategy Needs
As AI adoption accelerates, three elements of “talent” are more critical than ever: durable skills, emotional intelligence, and change management.And they have nothing to do with technology.
In the age of generative AI, agents, and other AI accelerators, the biggest threat to teams isn’t obsolescence, it’s underestimating the human factor. You have to think about tools and talent — both must evolve together.
As AI adoption accelerates, three elements of “talent” are more critical than ever: durable skills, emotional intelligence, and change management.
Durable Skills: The New “Hard Skills”
Durable skills are the utility players — things like critical thinking, communication, adaptability, problem-solving, and collaboration. They’re essential and independent of the tool or the context. They don’t expire with your next software update.
Why do you need durable skills now?
AI handles discrete tasks well. Context, nuance, or ambiguity? Not so much.
AI has the potential to flood the organization with output. Durable skills help teams make sense of it.
For example, AI can summarize the decisions made in a meeting, but only a person can interpret the implications of those decisions across real, specific stakeholder groups. Only a person can translate decisions into culturally consistent communications that land and resonate. Only a person can anticipate which stakeholders might resist or be early adopters of the changes to come.
Teams that lack durable skills may misuse AI, underuse AI, or misinterpret its outputs.
Emotional Intelligence: The Human Edge in the Age of Machines
Emotional Intelligence (EI) is the ability to recognize, understand, and manage the emotions of yourself and others. In an organizational context, we use emotional intelligence to influence, persuade, motivate, and manage others.
Why do you need emotional intelligence now?
AI without EI is doomed to failure. AI is a big change; moreover, it feels like a big change to people, because it’s such a hot topic. Are people afraid of being replaced or overwhelmed? News that AI is entering the workplace can trigger fear, confusion, and disengagement.
That’s why you need high-EI leaders during your AI rollout. They have the ability to detect unspoken cues (tone, silence, nervous behaviors), acknowledge them in a constructive way, convey information with sensitivity, and ultimately turn negative reactions into excitement and momentum.
But beyond the launch, you need AI to be a tool and a partner. One of the reasons for AI is to elevate your teams’ performance, right? Then you need synergy between employees and their AI agents. That’s where EI comes in. Emotionally intelligent teams promote curiosity and create the psychological safety necessary for risk-taking and innovation.
Change Management: The Accelerator (or Brake) on AI Success
Change Management includes:
- Leaders aligned on a clear vision and a compelling message for the change.
- Stakeholder engagement from the start.
- A detailed understanding of the impacts on each stakeholder group.
- Ways to engage the workforce and bring them from resistance to momentum to adoption to performance.
- Training that includes both the “why” and the “how.”
- Ways to sustain engagement and performance after launch.
Why do you need change management now?
Resistance to new technology is normal. Resistance to AI is certain. Ignoring it is fatal.
AI is a technology change, a process change, a mindset shift, and a performance challenge all in one. It’s a new way of working. It needs change management.
And, because AI is uncharted territory for most organizations, AI change management has to be current, nimble, and handled by your sharpest change agents.
AI doesn’t eliminate the need for people; it raises the bar for what people need to do well. No wonder some find it scary. Winning organizations are the ones that deeply value people and the unique skills they bring to the AI-enabled organization.
Want to explore the topic in more detail? We’d love to chat: Grab a virtual coffee together
-
Helping Your Workforce Adapt to AI
Four Practical Tips for Lasting Behavior Change.Four Practical Tips for Lasting Behavior Change.
Artificial intelligence is no longer a futuristic concept; it’s a present-day force reshaping industries, job functions, and workflows across the board.
Organizations often invest heavily in technology but overlook the most important part of successful adoption: people. The trouble is, while AI tools evolve at lightning speed, human behavior doesn’t change overnight.
To make AI truly work for the business, companies must help employees shift how they think, work, and collaborate.
That means addressing the fears, habits, and uncertainties that often accompany technological disruption.
Here are four practical ways to lead your workforce through this transition, building confidence, capability, and commitment along the way.
Involve employees early and often.
Change is easier when people feel seen and heard. Involve employees early, during the design, testing, and rollout of AI initiatives.
Ask what they need, what gets in their way, and how they imagine AI enhancing — not replacing – their talents and contributions. Co-creation builds trust and fosters ownership, turning skeptics into champions.
Give them ongoing, practical education.
Demystify AI from the start. Many employees hesitate because they don’t understand what AI is or how it applies to them.
Provide hands-on learning that lets people explore AI tools within the flow of their actual work. Encourage experimentation in low-risk environments and embed education into everyday tasks. When people understand the tools, fear gives way to curiosity, and resistance turns into engagement.
Highlight tangible, everyday value.
People adopt new behaviors when they see clear benefits. Don’t leave AI as an abstraction — show how it solves real problems.
Demonstrate how it reduces repetitive tasks, or speeds up decisions, or frees time for creative and strategic work. Use whatever example resonates with the employee. Connect AI directly to day-to-day responsibilities and you’ll build momentum from the ground up.
Anchor AI to strategic goals.
Behavior change sticks when it’s aligned with the company’s broader mission.
Tie AI initiatives to strategic goals like improving customer experience, boosting productivity, or accelerating innovation. And communicate that alignment clearly. When employees see how AI supports the company’s direction, they’re more motivated to adapt and contribute.
AI disruption doesn’t have to feel like a threat. It can be a powerful catalyst for growth when paired with intentional, human-centered change strategies.
By equipping your people with the knowledge, tools, and context they need, you’ll not only ease the transition, but you’ll unlock the full potential of your technology investment. The future of work isn’t just automated. It’s collaborative, strategic, and deeply human.